As best way to automate pcap collection takes center stage, this opening passage beckons readers into a world crafted with good knowledge, ensuring a reading experience that is both absorbing and distinctly original.
The topic of pcap collection has gained significant attention in recent years, especially in the realm of network security and analysis. With the increasing need for efficient and automated pcap collection, this article aims to provide valuable insights and practical guidance for IT professionals and network enthusiasts alike.
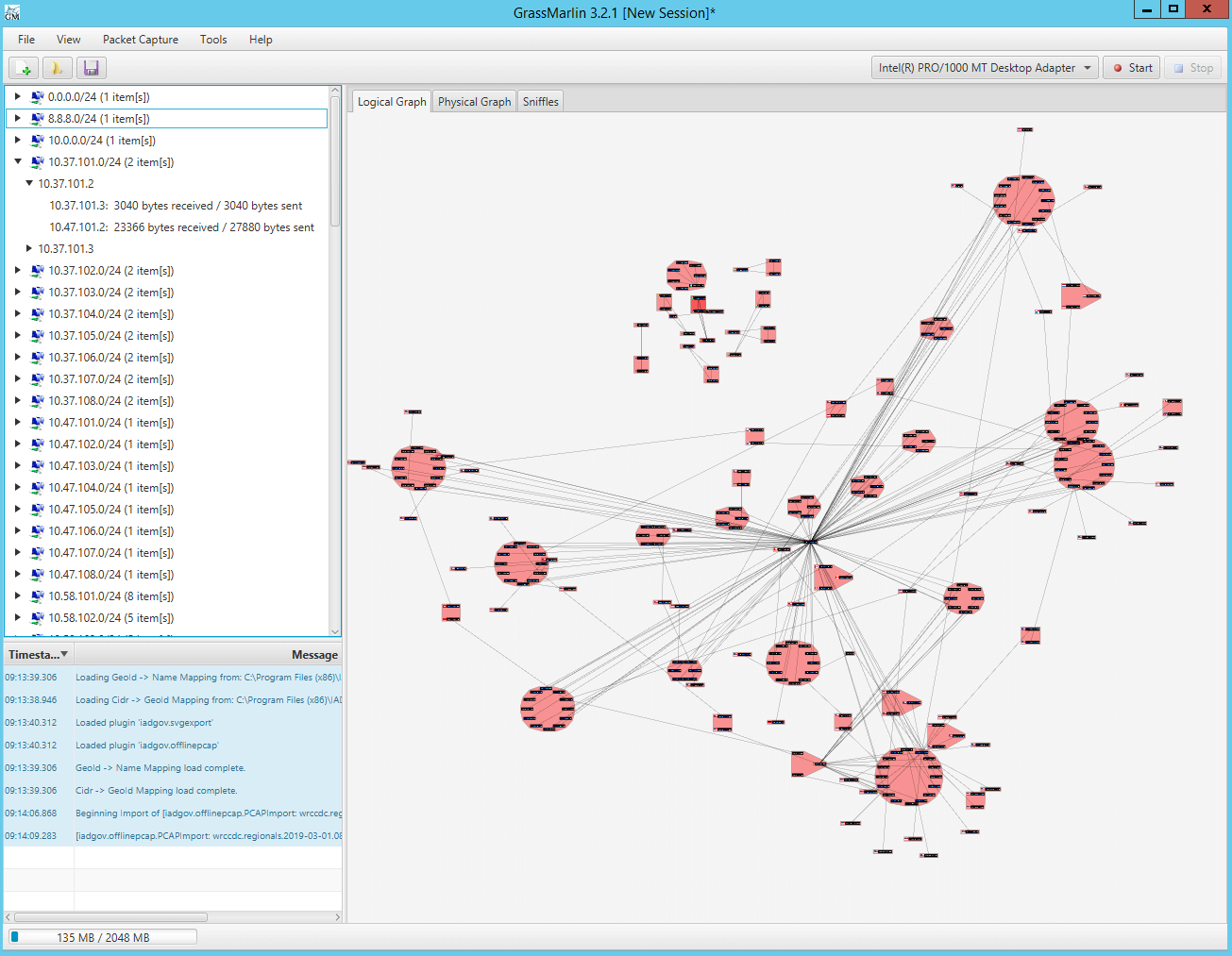
Implementing a Network Architecture for Efficient Pcap Collection

Implementing a robust and efficient packet capture system is crucial for network monitoring, security analysis, and forensic investigations. A well-designed network architecture can ensure that pcap collection is handled seamlessly, without introducing latency or impacting network performance. This discussion will focus on building a high-performance packet capture system, comparing centralized vs. decentralized approaches, and visualizing a medium-sized enterprise network topology.
Key Components for Building a High-Performance Packet Capture System
A high-performance packet capture system requires careful selection and configuration of several key components, including:
- Network Interface Cards (NICs): Dedicated NICs with high-throughput and low-latency capabilities are essential for capturing packets efficiently. Popular options include Intel X520 and Intel XL710.
- Packet Capture Software: Software such as Tcpdump, Tshark, and Wireshark provide a flexible and feature-rich packet capture and analysis environment.
- Storage Infrastructure: A scalable storage solution, using technologies like SAN or NAS, ensures that captured packets are stored efficiently, reducing latency and data loss.
- Redundancy and Failover: Implementing redundancy and failover mechanisms ensures continuous network operation and minimizes data loss in case of hardware or software failures.
Centralized vs. Decentralized Packet Capture Approaches
When designing a packet capture system, organizations can choose between a centralized or decentralized approach. Here are the benefits and trade-offs of each approach:
Centralized Approach:
- Efficient resource utilization, reducing the overall cost of ownership.
- Simplified management and monitoring tools.
- Streamlined storage and backup processes.
However, centralized packet capture can lead to:
- Single point of failure, introducing potential for data loss.
- Bottlenecked network traffic, impacting overall network performance.
Decentralized Approach:
- Redundant and fault-tolerant design, minimizing data loss.
- Improved network performance, as packets are captured closer to edge devices.
- Simplified troubleshooting and analysis.
However, a decentralized approach can result in:
- Increased complexity and higher overall cost.
- Potentially fragmented storage and management.
Network Topology Diagram: Medium-Sized Enterprise
| Device | Role | Description |
|---|---|---|
| Campus Switch | Connects to the core switch and multiple distribution switches to enable high-speed traffic routing. | |
| Distribution Switch | Provides Layer 3 routing functionality and connects to multiple access switches, ensuring network segments remain isolated. | |
| Access Switch | Connects user devices and enables Network Access Control (NAC), ensuring devices follow corporate policies and security standards. | |
| Network Tap | Injects a mirrored version of incoming traffic, enabling accurate packet capture and filtering without impacting the production network. | |
| Pcap Storage Server | Acts as a centralized repository for captured packets, providing real-time storage and data management for analysis and forensic purposes. |
Configuring Devices for Optimal Pcap Collection

Configuring devices for optimal pcap collection is a crucial step in ensuring that network packets are captured efficiently and accurately. This process involves setting up network interface cards (NICs) to intercept and store packets, which can then be analyzed using tools like Tcpdump or Wireshark. In this section, we will explore the step-by-step process for configuring a NIC for packet capture.
Step-by-Step Process for Configuring a NIC for Packet Capture
To configure a NIC for packet capture, follow these steps:
-
Open the device manager or network configuration settings on your system. This will allow you to access the properties of your NIC and adjust its settings.
-
Select the NIC you want to configure for packet capture and click on the “Properties” or “Advanced” tab. This will display a list of available settings.
-
Look for the “Promiscuous Mode” or “Receive All Packets” option and enable it. This will allow the NIC to capture all packets, not just those destined for the system.
-
Set the “Capture Filter” or “BPF Filter” to specify the types of packets you want to capture. For example, you can capture all TCP packets or only HTTP traffic.
-
Configure the “Packet Buffer Size” or “Ring Size” to ensure that the NIC can handle the volume of packets it will be capturing. A larger buffer size can handle more packets, but it may increase the risk of packet loss.
-
Apply the changes and start the packet capture process using a tool like Tcpdump or Wireshark.
Role of Packet Capture Libraries like libpcap and WinPcap, Best way to automate pcap collection
Packet capture libraries like libpcap and WinPcap play a crucial role in facilitating network sniffing. These libraries provide a standardized interface for capturing and analyzing network packets, making it easier to develop applications that can capture and analyze packet data.
libpcap: A widely-used, open-source packet capture library that provides a unified interface for capturing and analyzing packet data.
WinPcap: A packet capture library developed by CACE Technologies (now part of Riverbed Technology) that provides a Windows-specific interface for capturing and analyzing packet data.
These libraries offer a range of functionality, including:
- Capture packet data from a network interface
- Apply filters to select specific types of packets
- Analyze packet data using built-in tools or APIs
- Save captured packet data to a file for later analysis
Importance of Proper Permissions and Access Control
Proper permissions and access control are critical when setting up packet capture on network devices. This ensures that sensitive data is protected, and unauthorized access is prevented.
Best Practices for Security and Data Integrity
- Use a separate user account with limited privileges to run packet capture tools
- Configure access control lists (ACLs) to restrict access to sensitive network segments
- Use encryption to protect captured packet data
- Implement logging and auditing to monitor packet capture activity
Outcome Summary: Best Way To Automate Pcap Collection
In conclusion, automating pcap collection can streamline network analysis and security efforts, saving time and resources while providing valuable insights. By employing the techniques and tools Artikeld in this article, you can take your network analysis to the next level and stay one step ahead of threats.
FAQ Guide
What is pcap collection and its importance in network analysis?
PCAP (Packet Capture) collection is the process of capturing and storing network traffic for analysis and security purposes. It is crucial in network analysis as it helps identify network issues, security threats, and inefficiencies.
What is the best software for pcap collection?
While there are many software options, Wireshark, Tcpdump, and PcapPlusPlus are popular choices among network enthusiasts and security professionals. Each has its strengths and weaknesses, so it’s essential to choose the best fit for your specific needs.
Can I use open-source software for pcap collection?
Yes, open-source software like libpcap, WinPcap, and Tcpdump are widely used for pcap collection. They offer excellent performance, cost-effectiveness, and community-driven development.