Delving into best books on opsec is like embarking on a thrilling adventure, where the lines between fiction and reality blur, and the art of operational security is revealed in all its complexity.
From espionage novels that grip our imagination to sci-fi epics that imagine a future where opsec has evolved in unprecedented ways, literature offers a unique perspective on this critical concept, revealing both the successes and failures of those who have mastered the art of staying secret.
The Fundamentals of Operational Security in Literature – Explain the importance of opsec in books that explore real-world scenarios, providing at least 3 examples from different genres.
OpSec has become an essential aspect of modern literature, particularly in real-world scenario novels. This aspect of security plays a crucial role in keeping characters and readers informed on the significance of protecting sensitive information from potential threats. Through various examples, this fundamental principle can be illustrated to better understand its application in real-world contexts.
The concept of Operational Security is often portrayed in fiction as a vital tool for characters to protect their lives, missions, and organizations. By employing these measures, characters can increase their chances of success and mitigate risks. Examples from different genres showcase the significance of OpSec in preventing potential security breaches.
OpSec in Action: Real-World Scenarios in Literature
In the novel “The Bourne Series” by Robert Ludlum, the main character Jason Bourne, a highly trained CIA assassin, faces numerous challenges related to OpSec breaches. Through his journey, it becomes clear that Bourne’s failure to maintain proper OpSec procedures puts him and others at risk of being caught and exposed. This series exemplifies the importance of managing sensitive information and maintaining a secure online presence.
John Grisham’s novel “The Firm” highlights the dangers of OpSec negligence. Mitch McDeere, the protagonist, lands a highly paid job at a prestigious law firm but soon discovers that the organization is involved in organized crime and money laundering. As Mitch navigates this complex web, he realizes that maintaining OpSec protocols is crucial to protecting his life and exposing the firm’s corrupt activities.
The thriller “Tinker, Tailor, Soldier, Spy” by John le Carré delves into the world of espionage, where character relationships and OpSec protocols can be the difference between success and capture. George Smiley, a retired MI6 agent, is re-recruited to investigate a mole within the British intelligence community. The novel showcases the risks of OpSec breaches and the consequences for the characters involved.
Protagonist Agency and OpSec Success/Failure
The portrayal of protagonist agency in OpSec scenarios is a crucial aspect of these novels. When characters have varying levels of knowledge and skills in OpSec protocols, their actions and consequences can differ significantly.
Protagonist agency in novels highlights the importance of OpSec measures in keeping characters safe and the risks associated with neglecting them. For example, Jason Bourne’s extensive CIA training makes him more aware and skilled in OpSec compared to other characters in the series, which significantly affects the outcome of his missions. His expertise enables him to adapt swiftly to different OpSec situations and mitigate potential breaches.
Common OpSec Failures and Consequences
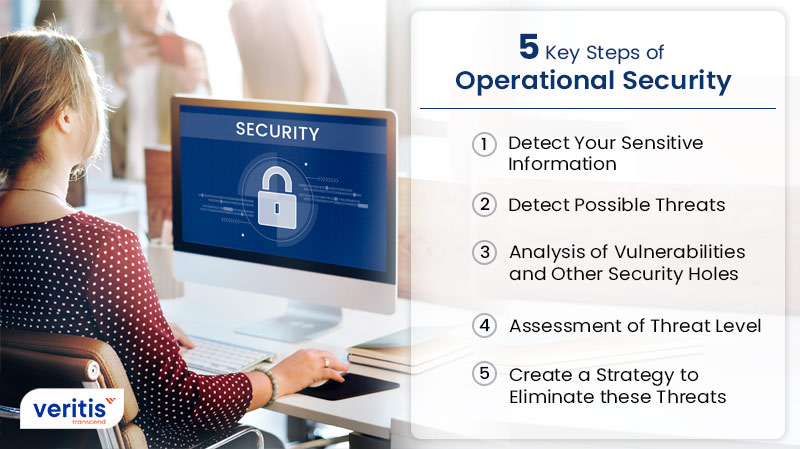
Real-world scenarios often depict the consequences of OpSec failures. Some common failures include:
- Lack of encryption and secure communication: Exposing sensitive information through insecure methods, such as unsecured email or online chat platforms.
- Using public networks for sensitive activities: Connecting to public Wi-Fi networks to access sensitive information or conduct critical activities.
- Failing to maintain secure passwords and account management: Using weak or reused passwords across multiple accounts and neglecting to update or manage them properly.
In literature, failure to employ these fundamental OpSec strategies can lead to catastrophic consequences for characters, making it essential to understand and adopt proper security protocols to prevent such breaches.
OpSec in Real-World Contexts
Through these examples and the portrayal of protagonist agency, it becomes clear that OpSec has a crucial impact on real-world scenarios and the stories told through literature. Whether it’s a real-world intelligence operation, a fictional novel, or a personal online presence, understanding and applying proper OpSec protocols can make all the difference in keeping sensitive information secure and mitigating potential threats.
Illustrating the Dangers of OpSec Breaches
In “The Bourne Series,” author Robert Ludlum often uses graphic descriptions of torture and other forms of retribution suffered by characters who fail to maintain proper OpSec measures. This vivid depiction serves as a warning to readers of the consequences of neglecting OpSec principles.
“You have to take care of the little things, like your life.” – Jason Bourne
Through novels, it is evident that maintaining proper OpSec is not only a matter of protecting oneself and one’s organization but also a matter of survival.
Real-World Implications
The portrayals of OpSec failures and their consequences in literature have far-reaching implications for readers. Understanding the risks associated with neglecting OpSec protocols can encourage readers to adopt and practice proper security measures in their personal and professional lives.
By illustrating the importance of OpSec through real-world scenarios, literature can provide valuable lessons for readers. The examples and portrayals of protagonist agency serve as reminders of the significance of protecting sensitive information and maintaining a secure online presence.
Deception and Misdirection in Bestselling Novels: Best Books On Opsec
Deception and misdirection are fundamental concepts in operational security (opsec), and bestselling novels often employ these tactics to deceive readers. By analyzing popular books, we can see how authors use opsec concepts to create suspense, surprise, and keep readers guessing. In this section, we will explore how authors use deception and misdirection to engage readers and discuss the impact of an unreliable narrator on opsec in a story.
Deception and misdirection can take many forms, from subtle hints and foreshadowing to outright lies and red herrings. In the novel “Gone Girl” by Gillian Flynn, the author masterfully uses deception and misdirection to create a suspenseful and twisty plot. Flynn manipulates the reader’s perceptions by using an unreliable narrator, Amy Dunne, who presents herself as a victim of her husband’s infidelity. However, as the story unfolds, it becomes clear that Amy is not what she seems, and Flynn expertly drops clues throughout the book to mislead the reader.
Another example of subtle misdirection can be seen in the novel “The Girl with the Dragon Tattoo” by Stieg Larsson. The author uses a complex web of characters and plot twists to keep the reader guessing. Larsson masterfully drops hints throughout the book to mislead the reader about the true identity of the killer and the motivations behind the murder.
Unreliable narrators can be a powerful tool for creating suspense and misdirection in a story. By manipulating the reader’s perceptions, authors can create a sense of uncertainty and tension. However, when used effectively, unreliable narrators can also add depth and complexity to a story, making it more engaging and memorable.
Impact of Unreliable Narrators on Opsec
An unreliable narrator can be a powerful tool for misdirection and deception in a story, but it requires careful management to avoid confusing the reader. When used effectively, an unreliable narrator can:
- Create suspense and tension by manipulating the reader’s perceptions
- Add depth and complexity to a story by creating multiple layers of meaning
- Keep the reader guessing and engaged by dropping subtle clues and hints
- Challenge the reader’s assumptions and biases by presenting a biased or distorted view of events
However, an unreliable narrator can also backfire if not managed carefully. When used poorly, an unreliable narrator can:
- Confuse the reader and create unnecessary complexity
- Lead to plot holes and inconsistencies
- Make the reader feel manipulated or deceived, rather than engaged and invested in the story
Effective use of an unreliable narrator requires careful consideration of the reader’s experience and needs. By manipulating the reader’s perceptions in a controlled and deliberate way, authors can create a suspenseful and engaging story that keeps readers guessing and invested until the end.
Historical Events as a Backdrop for Opsec Discussions
Historical events can be a powerful backdrop for opsec discussions in fiction. Many bestselling novels use historical events as a starting point for exploring opsec concepts, such as surveillance, infiltration, and counterintelligence.
For example, the novel “The Night Agent” by Matthew Quirk is based on the real-life events of the Watergate scandal. Quirk uses historical events as a backdrop for exploring opsec concepts, such as surveillance and infiltration, in a thrilling and suspenseful plot.
- Historical events provide a rich and authentic backdrop for opsec discussions
- Real-world events can add complexity and depth to a story
- Using historical events as a starting point can help authors create a sense of tension and urgency
- Authenticity and accuracy are crucial when using historical events in a story
Counterintuitive Opsec Strategies in Realistic Fiction
In the realm of realistic fiction, authors often employ unconventional operational security (opsec) strategies to create tension, surprise, and authenticity. These counterintuitive approaches deviate from conventional practices, making them more fascinating and challenging for readers. By analyzing these strategies, we can gain insights into the complexities of opsec and the importance of adapting to ever-changing environments.
The Art of Blended Invisibility
In the novel “The Bourne Identity” by Robert Ludlum, the protagonist, Jason Bourne, employs a counterintuitive opsec strategy by blending into his surroundings. Rather than trying to remain invisible, Bourne creates a new identity and becomes a part of the community, making it difficult for his enemies to detect him. This approach is similar to the concept of ” camouflage” in military operations, where troops blend into their environment to evade detection.
This approach can be applied in real-world scenarios where individuals need to remain undetected in a populated area. By studying the behaviors and habits of the local population, they can merge with the crowd, making it difficult to identify them.
Misadventures of Undercover Operations
In the novel “The Ipcress File” by Len Deighton, the protagonist, Harry Palmer, undergoes an undercover operation to uncover a plot by the Soviet Union to develop a mind-control device. Palmer’s opsec strategy involves infiltrating the Soviet organization by posing as a low-ranking officer, gathering information, and sending cryptic messages to his handler. However, his efforts are repeatedly thwarted by his own ineptitude and the paranoia of those he is spying on.
This approach highlights the risks and challenges associated with undercover operations. The success of such a mission relies heavily on the agent’s ability to maintain their cover, which can be compromised by their own emotions, personal biases, or the unpredictability of the situation.
The Power of Red Teams, Best books on opsec
In the novel “The Devil’s Banker” by Gerald Seymour, the protagonist, a former soldier, returns to his native Wales to investigate the activities of a British security firm that has become embroiled in a smuggling operation. The protagonist, aided by a “red team,” uses a counterintuitive opsec strategy by infiltrating the organization and gathering information from within. The red team is a group of operatives who pose as potential accomplices to gain the trust of the firm’s leaders.
This approach can be applied in real-world scenarios where individuals need to infiltrate an organization to gather information or prevent illicit activities. By studying the organization’s dynamics, they can create a cover story and build trust with the individuals involved.
The Importance of Context Awareness
In the novel “The Spy with No Name” by Daniel Silva, the protagonist, Gabriel Allon, employs a counterintuitive opsec strategy by focusing on the context of the situation rather than the specific details of the operation. He understands the motivations, emotions, and biases of the individuals involved, allowing him to anticipate and adapt to changing circumstances. This approach enables him to remain one step ahead of his enemies, even when conventional opsec practices fail.
This approach highlights the importance of context awareness in opsec. By understanding the nuances of human behavior and the intricacies of the environment, individuals can develop effective opsec strategies that take into account the complexities of the situation.
Opsec in the Digital Age

The rise of digital communication has transformed the way we live, work, and interact with each other. In this realm, Operational Security (Opsec) has evolved from a niche concern to a critical necessity for protecting identity and information. As digital communication channels continue to grow in importance, Opsec has become a pressing issue, requiring vigilance and proactive measures to safeguard digital communication channels and prevent information breaches.
The digital age has brought about both opportunities and challenges when it comes to Opsec. On one hand, digital communication channels have improved access to information and enabled global connectivity. On the other hand, these channels have created vulnerabilities that can be exploited by malicious actors, compromising individual and organizational security.
Protecting Digital Communication Channels
Opsec best practices emphasize the importance of protecting digital communication channels to prevent information breaches. Effective measures include using secure communication protocols, employing encryption techniques, and adopting robust authentication and authorization processes. The following strategies can help safeguard digital communication channels:
- Implement Secure Communication Protocols: Use end-to-end encryption protocols, such as Secure Sockets Layer/Transport Layer Security (SSL/TLS) or Pretty Good Privacy (PGP), to protect data exchanged over digital channels.
- Employ Encryption Techniques: Utilize encryption methods, such as Advanced Encryption Standard (AES) or Elliptic Curve Cryptography (ECC), to safeguard sensitive data stored or transmitted over digital channels.
- Adopt Robust Authentication and Authorization Processes: Implement multi-factor authentication (MFA) and role-based access control (RBAC) to ensure that only authorized individuals can access digital communication channels.
Secure communication protocols, encryption techniques, and robust authentication and authorization processes are essential for protecting digital communication channels and preventing information breaches.
Preventing Information Breaches
Opsec strategies also focus on preventing information breaches by minimizing digital footprints and securing digital assets. Best practices include regular security audits, vulnerability assessments, and incident response planning. The following strategies can help prevent information breaches:
- Conduct Regular Security Audits: Perform regular security audits to identify vulnerabilities and weaknesses in digital communication channels and digital assets.
- Perform Vulnerability Assessments: Regularly assess digital assets for known vulnerabilities and address them before they are exploited by malicious actors.
- Develop Incident Response Plans: Establish incident response plans to address information breaches and minimize their impact.
Regular security audits, vulnerability assessments, and incident response planning are crucial for preventing information breaches and maintaining Opsec.
Comparing Effectiveness of Digital Opsec Tools and Techniques
Opsec tools and techniques vary in effectiveness, depending on the specific use case and requirements. Some tools, like virtual private networks (VPNs) and password managers, provide robust protection, while others, such as public key infrastructure (PKI) and digital rights management (DRM), provide more specialized functionality.
| Tool/Technique | Effectiveness | Use Case |
|---|---|---|
| Virtual Private Networks (VPNs) | High | Secure remote access and communication |
| Password Managers | High | Secure password storage and management |
| Public Key Infrastructure (PKI) | Medium-High | Secure authentication and authorization |
| Digital Rights Management (DRM) | Medium | Protected content and intellectual property |
This comparison highlights the varying effectiveness of Opsec tools and techniques, emphasizing the need for a combination of robust security measures to safeguard digital communication channels and prevent information breaches.
Conclusion
Opsec in the digital age has become a pressing concern, requiring vigilance and proactive measures to protect digital communication channels and prevent information breaches. Effective strategies include secure communication protocols, encryption techniques, robust authentication and authorization processes, regular security audits, vulnerability assessments, and incident response planning. By adopting and comparing Opsec tools and techniques, individuals and organizations can prioritize their digital security and maintain Opsec in an ever-evolving digital landscape.
Summary
As we reflect on the lessons from these best books on opsec, we’re reminded that operational security is an ongoing challenge that requires constant vigilance, creativity, and adaptability. Whether you’re a seasoned practitioner or just starting to learn, exploring these captivating stories and insights can inform your own approach and help you stay one step ahead of the game.
Clarifying Questions
What is operational security?
Operational security (opsec) refers to the practices and techniques used to protect sensitive information and maintain secrecy in various contexts, including espionage, military operations, and cybersecurity.
Why is opsec relevant in literature?
Opsec is explored in various literary genres, including espionage novels, sci-fi, and thrillers, as authors leverage these concepts to create engaging narratives and explore the human experience.
Can opsec strategies be adapted to real-life situations?
Yes, many of the opsec strategies and techniques described in literature can be applied to real-life situations, such as protecting digital identity, preventing information breaches, and maintaining secrecy in personal and professional contexts.