As which best describes the terrorist planning cycle takes center stage, this opening passage beckons readers into a world crafted with good knowledge, ensuring a reading experience that is both absorbing and distinctly original.
The terrorist planning cycle is a complex process that involves various stages and components. It is a sequence of events that terrorist organizations use to plan, prepare, and execute their attacks. This process is crucial to understand for counter-terrorism efforts to be effective.
The Terrorist Planning Cycle: A Complex Process
The terrorist planning cycle is a complex and intricate process that involves various stages and components. It is a dynamic and adaptive process that allows terrorist organizations to adjust their tactics and strategies in response to changing circumstances and environments. The process involves a range of activities, from initial planning and reconnaissance to logistical preparations and operational implementation.
The Reconnaissance Phase
The reconnaissance phase is a critical component of the terrorist planning cycle. During this phase, terrorist operatives gather information about potential targets, including their vulnerability, security measures, and potential impact. This information is used to determine the feasibility of the target and to identify potential opportunities for attack. The reconnaissance phase involves the use of various tactics, including surveillance, infiltration, and intelligence gathering.
The reconnaissance phase is typically conducted in a clandestine manner, using a range of techniques to gather information without being detected. This may involve the use of advanced technologies, such as drones or cyber attacks, to gather information about a target. Alternatively, terrorist operatives may conduct physical reconnaissance, using human intelligence gathers to gather information about a target.
Tactical Planning, Which best describes the terrorist planning cycle
Once the reconnaissance phase is complete, terrorist operatives will begin to develop a tactical plan for the attack. This plan will Artikel the specific details of the operation, including the target, the method of attack, and the timeline for the operation. The tactical plan will also identify the resources required to carry out the operation, including personnel, equipment, and logistics.
Tactical planning involves a range of considerations, including the potential impact of the attack, the security measures in place, and the potential for detection. Terrorist operatives will also consider the potential for collateral damage and the potential impact on non-combatants.
Logistical Preparations
Logistical preparations are a critical component of the terrorist planning cycle. During this phase, terrorist operatives will acquire the resources and equipment required to carry out the attack. This may involve the use of various techniques, including supply chain infiltration and cyber attacks to disrupt the logistics of the target.
Logistical preparations also involve the transportation of personnel and equipment to the target location. This may involve the use of various tactics, including smuggling and false documentation to avoid detection.
Operational Implementation
The operational implementation phase is the final stage of the terrorist planning cycle. During this phase, the terrorist operatives will put their plan into action, carrying out the attack on the target. This may involve the use of various tactics, including bombs, guns, or other forms of violence.
Operational implementation involves a range of considerations, including the potential for detection, the potential for collateral damage, and the potential impact on non-combatants. Terrorist operatives will also consider the potential for escalation and the potential for response from the targeted organization or government.
The Significance of Intelligence Gathering
Intelligence gathering is a critical component of disrupting the terrorist planning cycle. By gathering information about the terrorist organization and its operatives, law enforcement and intelligence agencies can identify potential threats and disrupt the planning cycle.
Intelligence gathering involves a range of techniques, including human intelligence, signals intelligence, and open-source intelligence. It may also involve the use of advanced technologies, such as drones and cyber attacks, to gather information about terrorist organizations.
Examples of Successful Counter-Terrorism Operations
There have been several successful counter-terrorism operations that have targeted the terrorist planning cycle. Some examples include:
– Operation Iraqi Freedom: This operation, conducted by US and coalition forces, targeted the terrorist planning cycle of extremist organizations in Iraq. The operation involved a range of tactics, including intelligence gathering, surveillance, and strike operations, to disrupt the planning cycle and prevent attacks.
– Operation Enduring Freedom: This operation, conducted by US and coalition forces, targeted the terrorist planning cycle of extremist organizations in Afghanistan. The operation involved a range of tactics, including intelligence gathering, surveillance, and strike operations, to disrupt the planning cycle and prevent attacks.
– The Raid on Osama bin Laden’s Compound: This operation, conducted by US Special Forces, targeted the terrorist planning cycle of Al-Qaeda leader Osama bin Laden. The operation involved intelligence gathering, surveillance, and a strike operation to disrupt the planning cycle and prevent attacks.
The Terrorist Planning Cycle: Evasion Strategies and Detection Techniques

The terrorist planning cycle often involves the use of various strategies and tactics to evade detection. Terrorist organizations employ a range of methods to conceal their identities, hide their plans, and avoid being detected by law enforcement and intelligence agencies. This section will explore the different strategies used by terrorists to evade detection and the techniques used to gather intelligence and detect their planning activities.
Terrorist organizations use various strategies to conceal their identities and hide their plans. One of the primary methods is the use of encryption and secure communication channels. Terrorists use encrypted messaging apps, email services, and other communication tools to hide their communication and planning activities from law enforcement and intelligence agencies.
The use of secure communication channels allows terrorists to coordinate their activities, share information, and plan their operations without being detected. However, the increasing use of encryption has also created new challenges for law enforcement and intelligence agencies. To counter this, agencies have developed new techniques and tools to detect and decrypt encrypted communication.
Encryption and Secure Communication Channels
Terrorist organizations use various encryption methods and secure communication channels to hide their communication and planning activities. Some of the common methods include:
- The use of encrypted messaging apps such as Telegram and Signal, which offer end-to-end encryption and secure communication.
- The use of secure email services such as ProtonMail and Tutanota, which offer end-to-end encryption and secure communication.
- The use of virtual private networks (VPNs) and other secure communication channels to hide their IP addresses and location.
The use of encryption and secure communication channels has become a significant challenge for law enforcement and intelligence agencies. To counter this, agencies have developed new techniques and tools to detect and decrypt encrypted communication.
Safe Houses and Concealed Locations
Terrorist organizations also use safe houses and concealed locations to hide their planning activities and evade detection. Safe houses are hidden locations used by terrorists to plan and coordinate their operations without being detected. These locations are often concealed from public view and may be located in remote areas or hidden within existing buildings.
- Safe houses may be located in remote areas or hidden within existing buildings.
- Terrorist organizations use various methods to conceal their safe houses, including the use of disguises, fake identities, and secure communication channels.
- Law enforcement and intelligence agencies use various techniques to detect and identify safe houses, including the use of surveillance, intelligence gathering, and forensic analysis.
The use of safe houses and concealed locations is a significant challenge for law enforcement and intelligence agencies. To counter this, agencies have developed new techniques and tools to detect and identify hidden locations.
Human Intelligence and Disruption
Human intelligence plays a critical role in disrupting the terrorist planning cycle. Human intelligence involves the collection and analysis of information from human sources, including informants, undercover agents, and other sources.
- Human intelligence is used to gather information about terrorist organizations and their planning activities.
- Human intelligence is used to identify and disrupt terrorist networks and cells.
- Human intelligence is used to gather information about terrorist leaders and key figures.
The use of human intelligence is a key component of disrupting the terrorist planning cycle. By gathering and analyzing information from human sources, law enforcement and intelligence agencies can identify and disrupt terrorist networks and cells, and prevent terrorist attacks from occurring.
The role of human intelligence in disrupting the terrorist planning cycle cannot be overstated. Human intelligence provides critical information and insights that can be used to gather intelligence, identify and disrupt terrorist networks and cells, and prevent terrorist attacks from occurring. By leveraging human intelligence, law enforcement and intelligence agencies can effectively counter the evolving tactics and strategies used by terrorist organizations to evade detection and plan their operations.
The Terrorist Planning Cycle: Diversity in Participation

The terrorist planning cycle often involves a complex network of individuals with diverse backgrounds and expertise. This heterogeneity is a key factor in the cycle’s success, as it allows terrorist organizations to exploit various skills, resources, and connections.
The recruitment process for terrorist organizations is a critical aspect of the planning cycle. Various individuals are targeted based on their skills, social connections, and emotional vulnerabilities. Key roles and responsibilities within the terrorist planning cycle include recruiters, financiers, and operatives.
Recruiters
Recruiters play a crucial role in identifying and approaching potential recruits. They are typically skilled individuals with strong social connections and emotional intelligence. Their primary responsibility is to persuade potential recruits to join the terrorist organization, often using tactics such as ideological manipulation, emotional appeals, and social pressure.
Financiers
Financiers provide the necessary funding for terrorist operations. They often have connections to organized crime or corrupt businesses and can utilize covert financial networks to transfer funds. Their role is critical in allowing the terrorist organization to execute its plans.
Operatives
Operatives are the individuals responsible for carrying out the terrorist attacks. They often have specialized skills, such as bomb-making or surveillance techniques, and may be recruited directly from the streets or within existing extremist groups. Their primary responsibility is to execute the terrorist plan effectively, often under the guidance of the recruiter or financier.
Characteristics of Individuals Who Are Most Likely to Be Recruited
Socio-economic Factors
Individuals from disadvantaged socio-economic backgrounds are more likely to be recruited by terrorist organizations. This is due to factors such as financial desperation, social isolation, and a sense of grievance against the state. For example, individuals from impoverished regions or those who feel disenfranchised by the existing social and economic systems may be more susceptible to recruitment.
Emotional Vulnerabilities
Emotional vulnerabilities, such as feelings of anger, frustration, or a sense of injustice, can make individuals more susceptible to recruitment. Terrorist organizations often exploit these emotional vulnerabilities to create a sense of purpose and belonging among their recruits.
Social Connections
Strong social connections and a sense of community are essential for terrorist recruitment. Individuals who feel a sense of belonging to a particular social group or community may be more likely to be recruited. For example, individuals who attend mosques or engage in social activism may be targeted by terrorist recruiters.
Impact of Cultural and Social Factors on the Terrorist Planning Cycle
Cultural and social factors play a significant role in shaping the terrorist planning cycle. For example:
Cultural Identities
Cultural identities can influence an individual’s susceptibility to terrorist recruitment. For instance, individuals who identify strongly with a particular religious or ethnic group may be more susceptible to recruitment.
Social Norms
Social norms can also impact the terrorist planning cycle. For example, an individual who is raised in an environment where violence is normalized may be more likely to engage in extremist activities.
Social Networks
Social networks can facilitate the spread of extremist ideologies and provide a conduit for terrorist recruitment. For instance, social media platforms can facilitate the creation and dissemination of terrorist propaganda, while online communities can provide a space for terrorist recruiters to connect with potential recruits.
Effective Counter-Terrorism Requires Coordination and Cooperation of Various Agencies and Stakeholders
Effective counter-terrorism requires the coordination and cooperation of various agencies and stakeholders, including law enforcement agencies, intelligence services, and community organizations. This collaboration is crucial in disrupting the terrorist planning cycle, as it enables the sharing of intelligence, resources, and expertise.
Types of Counter-Terrorism Organizations and Their Roles
There are various types of counter-terrorism organizations that play critical roles in disrupting the terrorist planning cycle. These include:
- Law Enforcement Agencies: Law enforcement agencies, such as police departments and border control agencies, are responsible for investigating and preventing terrorist activities. They work closely with intelligence services to share intelligence and coordinate operations.
- Intelligence Services: Intelligence services, such as CIA and MI6, gather and analyze intelligence on terrorist organizations and networks. They provide critical information to law enforcement agencies and policymakers to inform counter-terrorism strategies.
- Community Organizations: Community organizations, such as non-governmental organizations (NGOs) and community groups, play a vital role in preventing terrorist radicalization and recruitment. They work with local communities to promote counter-narratives and provide alternative livelihoods.
- Military Units: Military units, such as special forces and SWAT teams, are responsible for conducting counter-terrorism operations, including raids and arrests.
These organizations work together to disrupt the terrorist planning cycle by sharing intelligence, coordinating operations, and building trust with local communities.
Coordination Mechanisms for Information Exchange and Joint Operations
Effective coordination mechanisms are essential for information exchange and joint operations between agencies. These mechanisms include:
- Intelligence Sharing: Intelligence sharing involves the exchange of information between agencies, including intelligence reports, surveillance footage, and witness statements.
- Joint Operations: Joint operations involve the coordination of multiple agencies to conduct raids, arrests, and other counter-terrorism operations.
- Task Forces: Task forces are specialized teams that bring together experts from multiple agencies to investigate and disrupt terrorist activities.
- Crisis Management Centers: Crisis management centers are command centers that coordinate responses to terrorist threats and incidents.
These mechanisms facilitate collaboration and enable agencies to respond quickly and effectively to terrorist threats.
Building Trust and Credibility between Communities and Law Enforcement
Building trust and credibility between communities and law enforcement is critical in preventing the terrorist planning cycle. This involves:
Community Engagement
Engaging with local communities through outreach programs, community meetings, and cultural events can help to build trust and credibility.
Cross-Cultural Training
Providing cross-cultural training for law enforcement officers can help to bridge cultural gaps and improve communication with diverse communities.
Collaborative Policing
Collaborative policing involves working closely with local communities to address social and economic issues, such as poverty and unemployment, that can contribute to radicalization.
Accountability and Transparency
Ensuring accountability and transparency within law enforcement agencies can help to build trust and credibility with local communities.
By building trust and credibility, law enforcement agencies can prevent the terrorist planning cycle by reducing the spread of extremist ideologies and promoting counter-narratives.
Last Word
Understanding the terrorist planning cycle is crucial to preventing and disrupting terrorist activities. By knowing the stages and components of the cycle, we can develop effective counter-terrorism strategies to target the terrorist planning cycle. This, in turn, can help to prevent terrorist attacks and keep communities safe.
User Queries: Which Best Describes The Terrorist Planning Cycle
What is the primary goal of the terrorist planning cycle?
The primary goal of the terrorist planning cycle is to plan, prepare, and execute terrorist attacks to achieve the organization’s objectives.
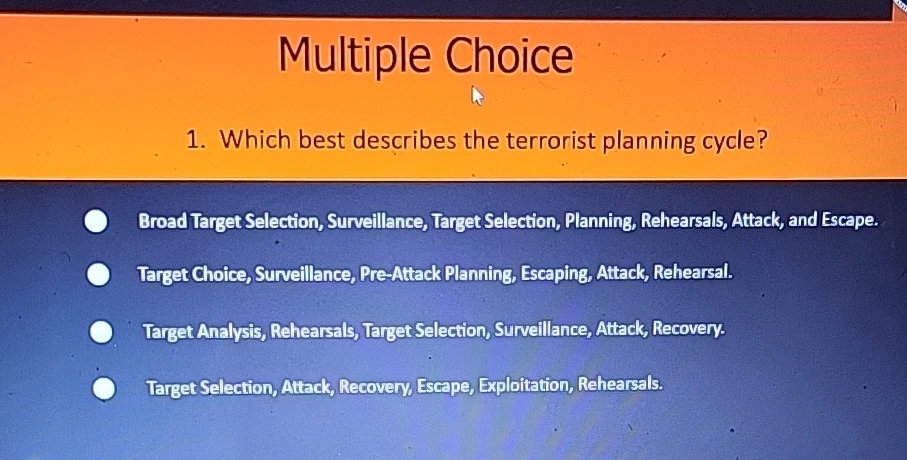
What are the stages of the terrorist planning cycle?
The stages of the terrorist planning cycle include reconnaissance, tactical planning, logistical preparations, and operational implementation.
What is the significance of intelligence gathering in disrupting the terrorist planning cycle?
Intelligence gathering is crucial in disrupting the terrorist planning cycle as it allows authorities to identify and track terrorist organizations and their plans.
What is the role of technology in the terrorist planning cycle?
Technology plays a significant role in the terrorist planning cycle, including the use of online platforms and social media to disseminate plans and gather support.
What is the importance of addressing the root causes of terrorism?
Addressing the root causes of terrorism, including radicalization and extremism, is crucial in preventing the terrorist planning cycle.