Which of the following are breach prevention best practices takes center stage, this opening passage beckons readers into a world crafted with good knowledge, ensuring a reading experience that is both absorbing and distinctly original.
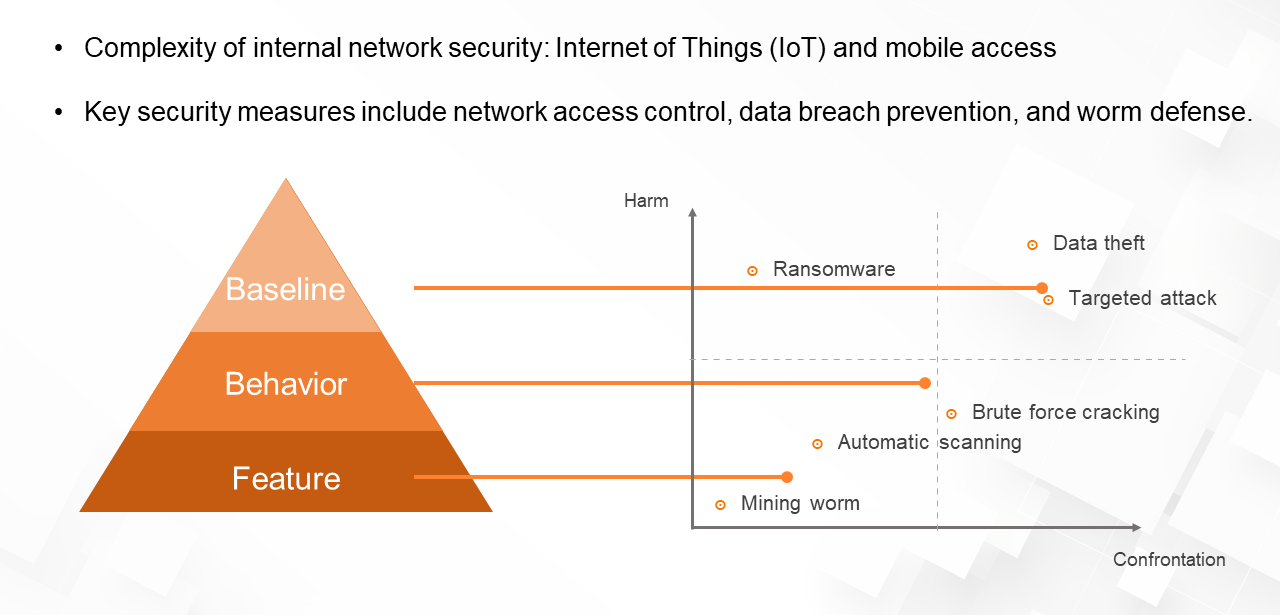
The content of which of the following are breach prevention best practices revolves around ten key areas: Implementing Robust Access Controls, Conducting Regular Security Audits, Establishing Incident Response Plans, Conducting Employee Education and Awareness Training, Implementing Secure Communication Protocols, Monitoring and Analyzing Security Threat Activity, Integrating Third-Party Risk Management, Creating and Maintaining Effective Data Classification, Conducting Background Checks, and Implementing Physical Security Controls. Each of these areas is crucial in preventing security breaches and ensuring a secure environment for any organization.
Conducting Regular Security Audits and Vulnerability Assessments
Conducting regular security audits and vulnerability assessments is a crucial step in identifying and mitigating potential security threats to your organization. By performing these assessments on a regular basis, you can ensure that your systems and networks are secure, and that any vulnerabilities or weaknesses are addressed before they can be exploited by attackers.
To begin with, it’s essential to define the scope of your security audits and vulnerability assessments. This involves identifying which systems, networks, and applications will be included in the assessment, and what types of vulnerabilities will be looked for. You should also determine the level of depth and breadth that your assessment will have, and whether it will be a manual or automated process.
Defining the Scope of Security Audits and Vulnerability Assessments
When defining the scope of your security audits and vulnerability assessments, you should consider the following factors:
- Scope: Determine which systems, networks, and applications will be included in the assessment. This may include servers, workstations, network devices, and web applications, among others.
- Vulnerability types: Decide which types of vulnerabilities you will look for during the assessment. This may include vulnerabilities related to software, hardware, or configuration issues.
- Level of depth: Determine the level of depth that your assessment will have. Will you be looking for low-level, high-risk vulnerabilities, or will you be focusing on lower-level vulnerabilities that are less likely to be exploited?
- Automated vs. manual: Decide whether your assessment will be conducted manually or automatically. Automated tools can be faster and more efficient, but may not catch as many errors or vulnerabilities.
Identifying Potential Vulnerabilities in Existing Systems
During the security audit and vulnerability assessment process, you will be looking for potential vulnerabilities in existing systems. This may involve using various tools and techniques, including penetration testing and risk assessment.
- Penetration testing: This involves simulating a real-world attack on your systems to identify vulnerabilities and weaknesses.
- Risk assessment: This involves evaluating the potential risks and consequences of a given vulnerability or weakness.
- Vulnerability scanning: This involves using automated tools to scan for potential vulnerabilities and weaknesses in your systems.
- Code review: This involves reviewing your code for potential vulnerabilities and weaknesses.
Evaluating and Prioritizing Identified Vulnerabilities
Once you have identified potential vulnerabilities in your systems, you will need to evaluate and prioritize them. This involves determining which vulnerabilities are most critical and need to be addressed first.
- Risk scoring: Assign a risk score to each vulnerability based on its potential impact and likelihood of exploitation.
- Vulnerability classification: Classify each vulnerability as high, medium, or low-risk, based on its potential impact and likelihood of exploitation.
- Prioritization: Prioritize vulnerabilities based on their risk score and classification.
Developing a Plan to Remediate Vulnerabilities
Once you have identified and prioritized vulnerabilities, you will need to develop a plan to remediate them. This may involve patching software, updating configurations, or changing security policies.
- Patch management: Develop a plan to patch software and fix vulnerabilities.
- Configuration changes: Develop a plan to update configurations and prevent vulnerabilities.
- Security policy changes: Develop a plan to change security policies and prevent vulnerabilities.
Regular security audits and vulnerability assessments are essential for identifying and mitigating potential security threats to your organization.
Conducting Employee Education and Awareness Training

Employee education and awareness training is a critical component of any effective security strategy, as it empowers employees to make informed decisions that mitigate the risk of security breaches. By educating employees about common security threats and best practices, organizations can significantly reduce the likelihood of successful attacks. This training should be tailored to address the specific security needs of the organization and its employees.
Importance of Employee Education and Awareness Training
Employee education and awareness training is essential for preventing security breaches because it helps employees understand the risks associated with their actions and the importance of following security protocols. By educating employees, organizations can reduce the likelihood of insider threats, such as accidental data breaches or intentional malicious activities. Furthermore, employee education and awareness training can also improve the overall security posture of the organization by promoting a culture of security awareness.
Examples of Effective Training Methods and Techniques
There are several effective training methods and techniques that can be used to educate employees about security risks and best practices. Some of these include:
– Scenario-based training, which presents real-life scenarios that employees may encounter and requires them to make informed decisions to resolve the situation.
– Interactive training, which engages employees through interactive activities, such as quizzes, games, or simulations, to convey complex security concepts in an engaging and memorable way.
– Role-playing, which allows employees to practice responding to security scenarios in a controlled environment, helping them develop the skills and confidence to respond effectively in real-world situations.
Key Security Topics to Cover during Employee Education and Awareness Training
The following are key security topics that should be covered during employee education and awareness training:
-
Proper Password Management
Password management is a critical aspect of security that employees must understand. This includes creating strong passwords, avoiding password reuse, and using two-factor authentication (2FA) where possible. Proper password management can prevent unauthorized access to sensitive data and systems.
- Passwords should be at least 12 characters long and include a mix of uppercase and lowercase letters, numbers, and special characters.
- Passwords should not be reused across multiple systems or applications.
- 2FA should be used whenever possible to provide an additional layer of security.
“A strong password is one that is unique, complex, and not easily guessable.”
-
Social Engineering Prevention
Social engineering is a type of attack that exploits human psychology and behavior to gain unauthorized access to sensitive data or systems. Employees must be educated on how to identify and prevent social engineering attacks, such as phishing and pretexting.
- Employees should be cautious when receiving emails or phone calls from unknown sources, especially if they request sensitive information or login credentials.
- Employees should verify the authenticity of requests for sensitive information or login credentials before responding.
- Employees should report any suspicious activity to the security team immediately.
“Social engineering attacks often rely on cleverly crafted emails or phone calls that manipulate employees into divulging sensitive information.”
-
Privacy and Data Protection
Employees must understand the importance of protecting sensitive data and maintaining confidentiality. This includes handling sensitive data with care, using secure transportation methods, and following data disposal procedures.
- Sensitive data should be handled with care to prevent exposure or loss.
- Sensitive data should be transported securely using encrypted media or secure online transfer methods.
- Data disposal procedures should be followed to ensure that sensitive data is properly erased or destroyed.
“Data protection is everyone’s responsibility, and employees must take steps to ensure that sensitive data is protected against unauthorized access or disclosure.”
-
Incident Response and Reporting
Employees must know how to respond to security incidents and report them to the security team. This includes identifying potential security risks, containing the incident, and cooperating with incident response efforts.
- Employees should report any potential security risks or incidents to the security team immediately.
- Employees should not attempt to contain the incident or investigate further without proper authorization.
- Employees should cooperate with incident response efforts and provide any necessary information or assistance.
“Incident response is a team effort, and employees must work together with the security team to contain and respond to security incidents.”
Creating and Maintaining Effective Data Classification and Labeling: Which Of The Following Are Breach Prevention Best Practices

Data classification and labeling play a crucial role in preventing breaches by ensuring that sensitive information is handled and stored securely. Effective data classification and labeling policies help organizations identify, categorize, and protect sensitive data, reducing the risk of unauthorized access, loss, or theft.
Proper data classification and labeling involve defining sensitivity levels and categorizing data types. This is essential for identifying and managing sensitive data, which includes confidential, sensitive, and restricted data. A well-structured data classification system ensures that sensitive data is stored, transmitted, and accessed according to strict security protocols.
Defining Sensitivity Levels
A robust data classification system begins with defining sensitivity levels. Sensitivity levels should be tailored to the organization’s specific needs and requirements. Common sensitivity levels include:
- Public: Information that is publicly available and can be shared with anyone.
- : Information that is only accessible to employees within the organization.
- Confidential: Information that requires special handling and access, such as employee personal data or business strategies.
- Restricted: Information that is heavily regulated, such as financial information or sensitive customer data.
Each sensitivity level should be accompanied by clear guidelines and procedures for handling and managing the associated data.
Categorizing Data Types
Categorizing data types is essential for identifying and managing sensitive data. Data types can be categorized based on their sensitivity levels. For instance, employee personal data, business strategies, and financial information are examples of high-sensitivity data that require special handling and access. On the other hand, publicly available information, such as company brochures or press releases, is considered low-sensitivity data and can be shared freely.
Designing a System to Track and Manage Data Labels
A robust system for tracking and managing data labels is crucial for ensuring the effective implementation of data classification and labeling policies. This includes procedures for data labeling, data anonymization, and data destruction. Data labels should be easily accessible and verifiable to prevent misclassification or unauthorized access.
Data Labeling Procedures
Data labeling procedures should be clearly defined and communicated to all employees. This includes guidelines for identifying sensitive data, applying data labels, and ensuring that data labels are accurately reflected in storage and transmission systems.
Data Anonymization Procedures
Data anonymization procedures are essential for protecting sensitive data. This includes procedures for removing identifiable information from data sets, such as names, addresses, and birthdates.
Data Destruction Procedures
Data destruction procedures are crucial for ensuring that sensitive data is no longer accessible or recoverable. This includes procedures for securely disposing of data storage devices, such as hard drives or USB drives.
Creating and maintaining effective data classification and labeling policies requires ongoing monitoring and evaluation. Regular security audits and vulnerability assessments can help identify areas for improvement and ensure that data classification and labeling policies remain effective in addressing breach prevention.
Conducting Background Checks and Continuous Monitoring on Employees
Conducting thorough background checks and continuous monitoring on employees is a vital aspect of preventing security breaches in an organization. With the increasing number of data breaches and cyber attacks, it is essential to ensure that employees do not pose a risk to the organization’s security. This involves verifying an employee’s identity, checking their background, and monitoring their behavior on the job.
In today’s digital age, employees have access to vast amounts of sensitive information, making them a potential threat to the organization’s security. A single malicious employee can compromise the entire system, causing irreparable damage. Conducting background checks and continuous monitoring can help identify potential risks and prevent them from becoming a reality.
Conducting Background Checks
Background checks involve verifying an individual’s identity, checking their employment history, and assessing their character. This can be done using various sources and tools, including:
– Government databases, such as the Federal Bureau of Investigation (FBI) and the National Crime Information Center (NCIC)
– Employment screening services, such as background check providers and credit reporting agencies
– Social media monitoring tools, to assess an individual’s online behavior
– Online reviews and ratings platforms, to assess an individual’s reputation
Using these sources and tools can provide valuable information about an individual’s background, helping to identify potential risks and make informed hiring decisions.
Continuous Monitoring
Continuous monitoring involves regularly checking an employee’s behavior and activity on the job. This can be done using various methods, including:
– Monitoring employee activity on the organization’s systems and networks
– Conducting regular security awareness training and phishing simulations
– Reviewing employee performance and progress regularly
– Conducting random security audits and vulnerability assessments
Continuous monitoring can help identify potential security risks and prevent them from becoming a reality.
Key Considerations for Employee Background Checks and Continuous Monitoring
The following table highlights key considerations for employee background checks and continuous monitoring:
| Frequency | Scope | Notes |
| — | — | — |
| Annual background checks | Verify identity, employment history, character | Use government databases, employment screening services, and social media monitoring tools |
| Quarterly security monitoring | Monitor employee activity, network activity | Use security information and event management (SIEM) systems and user activity monitoring (UAM) tools |
| Regular security awareness training | Educate employees on security best practices | Use phishing simulations and regular training sessions |
| Random security audits | Identify vulnerabilities and address them | Conduct regular vulnerability assessments and penetration testing |
| Regular performance reviews | Monitor employee performance and progress | Use regular reviews to identify areas for improvement |
Implementing Physical Security Controls to Prevent Unauthorized Access
In today’s digital age, physical security controls are often overlooked, but they play a crucial role in preventing unauthorized access to sensitive areas and assets. A robust physical security system can help deter potential attackers and protect against various threats, including terrorism, natural disasters, and human error. By implementing effective physical security controls, organizations can ensure the confidentiality, integrity, and availability of their data and assets.
Importance of Physical Security Controls in Breach Prevention, Which of the following are breach prevention best practices
Physical security controls are designed to prevent unauthorized access to an organization’s physical assets, including buildings, data centers, and sensitive equipment. These controls can help prevent breaches by blocking intruders’ access to sensitive areas, reducing the risk of data theft, sabotage, and other malicious activities. Effective physical security controls can also provide an additional layer of protection against insider threats, such as disgruntled employees or contractors.
Developing and Implementing Effective Physical Security Controls
To develop and implement effective physical security controls, organizations should consider the following measures:
- Access Control Systems: Install access control systems that can accurately register and monitor individual movements, including door sensors, motion detectors, and CCTV cameras.
- Secure Doors and Entrances: Ensure all doors and entrances are securely locked, and consider installing electronic door locks with swipe cards or biometric authentication.
- Surveillance Systems: Implement a comprehensive surveillance system that includes CCTV cameras with night vision, motion detection, and recording capabilities.
- Alarm Systems: Install alarm systems that can detect intruders and alert security personnel, and consider using smart alarm systems that can integrate with access control systems.
- Lighting: Ensure adequate lighting in all areas, particularly in dark or poorly lit areas, to prevent intruders from hiding.
Organizations should also consider conducting regular security audits and vulnerability assessments to identify potential weaknesses in their physical security systems and address them promptly. Regular maintenance and testing of physical security controls can help ensure they remain effective and functional.
Monitoring and Testing Physical Security Controls
To ensure the effectiveness of physical security controls, organizations should design a system to monitor and test these controls regularly. This can include:
- Regular Vulnerability Assessments: Conduct regular vulnerability assessments to identify potential weaknesses in physical security controls and address them promptly.
- Penetration Testing: Conduct penetration testing to simulate potential attacks and identify areas for improvement in physical security controls.
- Continuous Monitoring: Establish a continuous monitoring program to regularly review and update physical security controls to stay ahead of emerging threats.
By implementing a robust physical security system and regularly monitoring and testing these controls, organizations can reduce the risk of unauthorized access and breaches, ensuring the confidentiality, integrity, and availability of their data and assets.
Last Recap
which of the following are breach prevention best practices is a comprehensive guide that Artikels the essential steps to prevent security breaches. By following these best practices, organizations can significantly reduce the risk of security breaches and ensure a secure environment for their data. Remember, security is an ongoing process that requires constant monitoring and improvement.
FAQ Resource
What is breach prevention?
Breach prevention is the set of measures taken to prevent security breaches, including implementing access controls, conducting regular security audits, and establishing incident response plans.
Why is employee education and awareness training important?
Employee education and awareness training is crucial in preventing security breaches because employees are often the weakest link in an organization’s security. By educating employees about security risks and best practices, organizations can reduce the risk of security breaches.
What is the importance of data encryption?
Data encryption is essential in protecting sensitive data from unauthorized access. By encrypting data, organizations can ensure that even if data is compromised, it will be unreadable to unauthorized parties.