As which of the following best describes social engineering takes center stage, this opening passage beckons readers into a world of psychological manipulation, where the goal is to deceive individuals into divulging confidential information, without using any technical means.
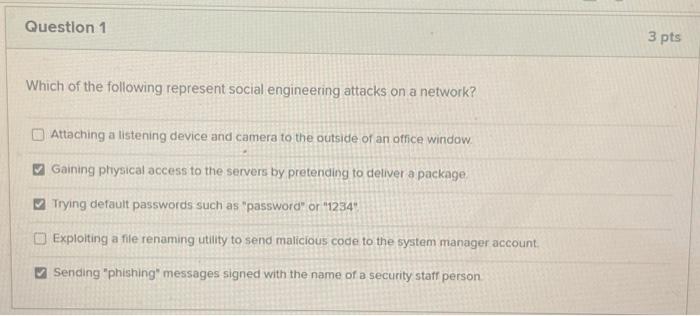
Social engineering, a form of psychological manipulation, exploits human psychology to achieve its goals. It employs various tactics, including phishing, pretexting, and baiting, to trick individuals into divulging sensitive information. Cognitive biases and heuristics play a crucial role in making social engineering attacks more effective, as they often target vulnerabilities in human psychology.
Social Engineering as a Form of Psychological Manipulation

Social engineering is a powerful tactic that leverages the vulnerabilities of human psychology to achieve malicious goals. By exploiting our emotions, biases, and heuristics, social engineers can gain access to sensitive information, disrupt critical systems, and manipulate individuals into performing specific actions. This form of psychological manipulation is used by various malicious actors, including cyber attackers, con artists, and even nation-state operatives.
One of the key aspects of social engineering is the exploitation of cognitive biases and heuristics. For instance, the
Confirmation Bias
leads people to seek out information that confirms their existing beliefs, while the
Availability Heuristic
causes them to overestimate the importance of information based on its ease of recall. By preying on these biases and heuristics, social engineers can create situations that appear convincing and urgent, making it more likely for victims to divulge sensitive information or perform unwanted actions.
Successful Psychological Manipulations
Social engineers have been successful in manipulating individuals through various tactics, including phishing, pretexting, and baiting. Here are 3 examples of successful psychological manipulations:
- In 2019, a group of attackers used a phishing email to trick a government employee into revealing sensitive information. The email was designed to appear as if it was sent by the employee’s supervisor, creating a sense of urgency and authority.
- In 2018, a social engineer convinced a bank employee to transfer $1.1 million to a fake account by posing as the bank’s CEO. The attacker used a convincing pretext and manipulated the employee into believing that the transfer was a routine operation.
- In 2017, a group of attackers used a baiting tactic to steal sensitive information from a company’s employees. They placed a USB drive containing malware in a public area, and an unsuspecting employee plugged it into their computer, allowing the attackers to gain access to the company’s network.
The Role of Cognitive Biases in Social Engineering
Cognitive biases play a significant role in making social engineering attacks more effective. By exploiting these biases, social engineers can create situations that appear convincing and urgent, making it more likely for victims to divulge sensitive information or perform unwanted actions. Here are some examples of how cognitive biases are used in social engineering:
-
The
Anchoring Bias
causes people to rely too heavily on the first piece of information they receive, even if it is incorrect. Social engineers use this bias by providing a convincing initial story or information that sets the tone for the rest of the interaction.
-
The
Foot-in-the-Door Technique
involves asking for a small favor initially and then gradually increasing the requests. Social engineers use this technique by asking for small pieces of information or favors, gradually increasing the requests until the victim divulges sensitive information.
A Hypothetical Scenario: A Social Engineer Targets an Unsuspecting Victim
Let’s imagine a scenario where a social engineer targets a young professional who works in a marketing firm. The social engineer sends an email purporting to be from the firm’s IT department, stating that the employee’s computer has been infected with malware and needs to be reset. The email includes a link to a convincing-looking support page that asks for the employee’s login credentials and other sensitive information.
The social engineer uses a combination of psychological manipulation and technical skills to make the email appear convincing. They use a convincing pretext, a well-designed email template, and a convincing story to manipulate the employee into divulging sensitive information.
Comparing the Effectiveness of Different Social Engineering Tactics
Different social engineering tactics have varying levels of effectiveness depending on the situation and the victims. Here’s a comparison of some common social engineering tactics:
| Tactic | Effectiveness |
|---|---|
| Phishing | High |
| Pretexting | Medium-High |
| Baiting | Medium |
The Importance of Social Engineering in Real-World Applications
Social engineering is not limited to cyber attacks; it’s also used in various real-world applications, including military operations, corporate espionage, and even in sales and marketing. Military operations use social engineering to gather intelligence, influence the behavior of adversaries, and disrupt enemy operations.
Corporate espionage uses social engineering to steal sensitive information, disrupt business operations, and gain a competitive advantage. Sales and marketing use social engineering to build relationships, convince customers to make purchases, and promote products.
Methods Used by Social Engineers to Gather Information
Social engineers employ various methods to gather information about their targets, often using psychological manipulation to build trust and extract sensitive data. These methods can be categorized into several key areas, each designed to exploit human vulnerabilities and gather specific types of information.
Open-Source Intelligence (OSINT)
Open-source intelligence involves gathering information from publicly available sources, such as social media profiles, online forums, and public records. Social engineers can create detailed profiles of their targets by analyzing these publicly available details, including their interests, habits, and relationships. For example, Facebook profiles can reveal a person’s birthday, hometown, and job, which can be used to guess their social security number or exploit their online behavior.
- Target’s social media profiles (e.g., Facebook, Twitter, Instagram)
- Public records (e.g., property deeds, court documents)
- Online forums and discussion groups
- Blogs and websites hosted by the target
- Reputation and review sites (e.g., LinkedIn, Yelp)
By combining information from these public sources, social engineers can create a rich profile of their target, which can be used to launch targeted phishing attacks, spear phishing, or social engineering scams.
Dumpster Diving
Dumpster diving involves searching through a target’s trash or recycle bins for sensitive documents and information. Social engineers may rummage through a target’s trash to find receipts, bank statements, or other financial records. This can lead to the theft of credit card numbers, social security numbers, or other personal data.
- Financial documents (e.g., bank statements, credit card receipts)
- Personal identification documents (e.g., driver’s license, passport)
- Business records (e.g., invoices, receipts)
Dumpster diving can be a lucrative way for social engineers to gather sensitive information without using technical hacking techniques.
Shoulder Surfing
Shoulder surfing involves watching a target as they enter sensitive information, such as a password or credit card number, into a device or computer. Social engineers may use this technique to steal login credentials, encryption keys, or other sensitive data. For example, a social engineer might sit behind a target as they enter their credit card number into an online store’s payment form.
Cold Reading, Which of the following best describes social engineering
Cold reading involves using psychology and body language to build rapport with a target and extract sensitive information. Social engineers may use cold reading techniques to convince a target that they are genuine and trustworthy, before asking for sensitive information.
Phishing
Phishing involves sending fake emails, texts, or messages to a target, pretending to be from a legitimate source (e.g., a bank, email provider). Social engineers may use phishing to steal sensitive information, such as login credentials or credit card numbers.
Physical Surveillance
Physical surveillance involves watching a target’s movements and activities in person. Social engineers may use this technique to gather information about a target’s daily routine, habits, and relationships.
Technology Facilitation
Advances in technology have made it easier for social engineers to gather information about their targets. For example, social media platforms have made it easier to gather information about a target’s online behavior, interests, and relationships. Additionally, phishing attacks can be launched using fake emails, texts, or messages that appear to be from a legitimate source.
Creating and Executing a Successful Social Engineering Attack
Social engineering attacks require a combination of psychological manipulation and technical skills to execute successfully. A convincing backstory and pretext are crucial elements in building trust with the target. By creating a fake persona, social engineers can gain access to sensitive information, systems, or networks.
The Importance of a Convincing Backstory and Pretext
A well-crafted backstory and pretext can help social engineers establish a sense of credibility and trust with their target. This is achieved by creating a fake persona that aligns with the target’s expectations and interests. For instance, a social engineer may pose as a IT technician or a high-ranking executive to gain access to sensitive information.
Hypothetical Scenario: Using a Fake Persona to Build Trust
Meet John, a social engineer who poses as a IT technician to gain access to a company’s network. John creates a fake email address and LinkedIn profile, where he lists his skills and experience as a IT technician. He then reaches out to the company’s IT department, claiming that he needs access to their network to perform a routine maintenance task. The IT department, unaware of John’s true intentions, grants him access to the network. Once inside, John begins to gather sensitive information, which he later uses for malicious purposes.
Technical Skills Required for Social Engineering Attacks
While a convincing backstory and pretext are essential, social engineers also require technical skills to execute their attacks. These skills include:
- Creating custom malware: Social engineers need to create malware that can bypass security controls and gain access to sensitive information. This requires a deep understanding of programming languages, such as Python or C++.
- Bypassing security controls: Social engineers need to know how to bypass security controls, such as firewalls and intrusion detection systems. This requires knowledge of networking protocols and security vulnerabilities.
- Using social engineering tools: Social engineers use specialized tools, such as social engineering frameworks and exploits, to carry out their attacks.
Case Study: A Successful Social Engineering Attack
In 2013, a social engineer posed as a FedEx employee to gain access to a UPS employee’s email account. The social engineer created a fake FedEx email address and contact information, claiming that UPS’s package had been delayed. The UPS employee, unaware of the scam, provided their login credentials to the social engineer, who then gained access to their email account. The social engineer used this access to steal sensitive information and disrupt UPS’s operations.
While social engineering attacks can be highly successful, there are several common mistakes that can lead to detection. These include:
- Taking too long to build trust: Social engineers need to establish trust with their target quickly to avoid raising suspicion.
- Using overly complex tactics: Social engineers should use tactics that are believable and realistic to avoid arousing suspicion.
- Failing to cover their tracks: Social engineers need to delete email trails, IP logs, and other digital evidence to avoid detection.
Case Studies of Real-World Social Engineering Attacks: Which Of The Following Best Describes Social Engineering
Throughout history, social engineering attacks have become increasingly sophisticated, often leading to devastating consequences. These attacks exploit human psychology, using tactics like fear, urgency, and scarcity to manipulate individuals into divulging sensitive information or performing certain actions. In this section, we will explore five real-world examples of successful social engineering attacks, examining the tactics and techniques used by the attackers.
1. The Target Corporation Breach (2013)
In 2013, a sophisticated social engineering attack targeted the payment processing systems of Target Corporation. Hackers stole the credit card information of over 40 million customers, causing significant financial losses and damage to the company’s reputation. To execute the attack, hackers gained access to Target’s networks through a third-party vendor, using spear phishing and other tactics to spread malware and create backdoors.
- Hackers gained access to Target’s network through a third-party vendor, using spear phishing and other tactics to spread malware and create backdoors.
- They stole credit card information from over 40 million customers, affecting sales and the company’s reputation.
- The breach led to significant financial losses, fines, and an overhaul of Target’s security measures.
2. The Dropbox Breach (2012)
In 2012, hackers launched a large-scale phishing attack against Dropbox users, using tactics like spoofed emails and fake login pages to steal sensitive information. The attack targeted more than 7,000 users, compromising their passwords and other data. The breach was notable for its scale and the ease with which hackers were able to deceive users.
- Hackers launched a large-scale phishing attack against Dropbox users, using spoofed emails and fake login pages to steal sensitive information.
- More than 7,000 users had their passwords and other data compromised in the breach.
- Dropbox responded by implementing new security measures and notifying affected users of the breach.
3. The Google Employee Phishing Attack (2009)
In 2009, hackers launched a targeted social engineering attack against Google employees, using tactics like spear phishing and fake emails to create backdoors into the company’s networks. The attack compromised the Gmail accounts of several Google employees, leading to a significant security overhaul.
- Hackers launched a targeted social engineering attack against Google employees, using spear phishing and fake emails to create backdoors.
- Several Google employees had their Gmail accounts compromised in the breach.
- Google responded by implementing new security measures and improving employee training on social engineering tactics.
4. The Facebook Spear Phishing Attack (2015)
In 2015, hackers launched a targeted social engineering attack against Facebook users, using tactics like spear phishing and fake emails to steal sensitive information. The attack targeted more than 100 million users, compromising their passwords and other data.
- Hackers launched a targeted social engineering attack against Facebook users, using spear phishing and fake emails to steal sensitive information.
- More than 100 million users had their passwords and other data compromised in the breach.
- Facebook responded by implementing new security measures and notifying affected users of the breach.
5. The Equifax Data Breach (2017)
In 2017, hackers launched a massive social engineering attack against Equifax, compromising the sensitive information of over 147 million customers. The attack targeted a vulnerability in Apache Struts software, which hackers exploited to gain access to Equifax’s networks.
- Hackers launched a massive social engineering attack against Equifax, compromising the sensitive information of over 147 million customers.
- The attack targeted a vulnerability in Apache Struts software, which hackers exploited to gain access to Equifax’s networks.
- Equifax responded by implementing new security measures and notifying affected users of the breach.
The Role of Technology in Social Engineering

In today’s digital age, technology plays a significant role in facilitating social engineering methods. Social engineers use various technologies to create and spread malware, phishing emails, and other types of social engineering attacks. These attacks can be highly effective, as many people are unaware of the ways in which technology can be used to manipulate them.
Creating and Spreading Malware
Social engineers use various types of malware to compromise computer systems and steal sensitive information. Malware can be spread through email attachments, infected software downloads, or even infected websites. Once malware is installed on a system, it can steal login credentials, credit card numbers, and other sensitive information.
- Malware can be designed to spread automatically, infecting multiple systems quickly.
- Malware can be programmed to steal specific types of data, such as login credentials or credit card numbers.
- Malware can be designed to remain undetected on a system, allowing the social engineer to continue to gather sensitive information.
Design of a Flowchart Illustrating the Process of Using Technology to Facilitate Social Engineering Attacks
Here is a general flowchart detailing the process of using technology to facilitate social engineering attacks:
1. Identify target: The social engineer identifies a target person or organization.
2. Gather information: The social engineer gathers information about the target, including their security protocols and vulnerabilities.
3. Create attack: The social engineer creates a social engineering attack, such as a phishing email or a malware attachment.
4. Distribute attack: The social engineer distributes the attack to the target, often through email or social media.
5. Steal information: The social engineer steals sensitive information from the target, often using malware to steal login credentials or credit card numbers.
Common Technologies Used by Social Engineers
Social engineers use a variety of technologies to facilitate their attacks, including:
- Social media: Social engineers use social media platforms to spread malware, phishing emails, and other types of social engineering attacks.
- Email: Social engineers use email to send phishing attacks and malware attachments to targets.
- Text messages: Social engineers use text messages to send phishing attacks and malware attachments to targets.
Guidelines for Using Technology Safely
To avoid falling victim to social engineering attacks, it’s essential to use technology safely. Here are some guidelines to follow:
- Avoid suspicious links and attachments: Never click on links or open attachments from unknown sources.
- Keep software up to date: Regularly update your software and operating system to ensure you have the latest security patches.
- Use strong passwords: Use strong, unique passwords for all of your online accounts.
- Be cautious with email and text messages: Be careful when opening email and text messages from unknown sources, as they may contain malware or phishing attacks.
Implementing Security Controls
To prevent technology-enabled social engineering attacks, it’s essential to implement security controls. Here are some ways to do so:
- Use firewalls: Firewalls can help block incoming and outgoing network traffic, preventing malware from spreading.
- Use antivirus software: Antivirus software can help detect and remove malware from your system.
- Implement two-factor authentication: Two-factor authentication requires users to enter a second form of verification, such as a code sent to their phone, in addition to their password.
The Psychology Behind Social Engineering
Social engineering attacks rely on exploiting human psychology to manipulate individuals into divulging sensitive information or performing certain actions. Understanding the psychological motivations behind these attacks can help prevent their success. One of the most effective tactics used by social engineers is creating a sense of urgency, fear, or scarcity to prompt individuals into making hasty decisions. By recognizing these tactics and understanding the underlying psychological principles, individuals can better protect themselves against social engineering attacks.
Designing a Flowchart for the Psychological Process Underlying Social Engineering Attacks
A flowchart illustrating the psychological process can help visualize the sequence of events that lead to a successful social engineering attack. The following is a simplified representation of the flowchart:
Identify victim • Establish rapport • Create sense of urgency/fear/scarcity • Exploit psychological biases/heuristics • Perform malicious action
This flowchart highlights the key stages in the psychological process that social engineers use to manipulate individuals.
5 Common Psychological Biases and Heuristics that Make Social Engineering Attacks More Effective
Certain psychological biases and heuristics can make individuals more susceptible to social engineering attacks. Here are five common biases and heuristics:
- Social Proof: People tend to trust others who are like them or are part of an in-group. This can make individuals more likely to follow the advice or guidance of someone they perceive as a peer.
- Anchoring Bias: Individuals tend to rely too heavily on the first piece of information they receive, even if it is biased or incorrect. This can lead to a loss of critical thinking and a failure to consider alternative perspectives.
- Confirmation Bias: People tend to seek out information that confirms their pre-existing beliefs and neglect information that contradicts them. This can make individuals more vulnerable to social engineering attacks that play on their fears or biases.
- Reciprocity Bias: When individuals receive something for free, they tend to feel a sense of obligation to repay the favor in some way. This can be exploited by social engineers who provide “free” information or services in return for sensitive data.
- Loss Aversion: People generally fear losses more than they value gains. This can make individuals more susceptible to social engineering attacks that appeal to their fear of losing something valuable.
Guidelines for Recognizing and Addressing Psychological Biases and Heuristics in Yourself and Others
Recognizing and addressing psychological biases and heuristics is crucial for preventing social engineering attacks. Here are some guidelines to help you recognize and address these biases in yourself and others:
- Practice critical thinking: Approach new information with a critical eye, considering multiple perspectives and evaluating evidence before making a decision.
- Seek diverse input: Expose yourself to diverse viewpoints and opinions to broaden your understanding and reduce the influence of confirmation bias.
- Be aware of your emotional state: Recognize when you are feeling emotional or under stress, as this can increase your susceptibility to social engineering attacks.
- Verify information: Before acting on any information, verify it through multiple sources to reduce the impact of anchoring bias.
- Educate others: Teach others about psychological biases and heuristics to help them become more aware of these tendencies and better equipped to defend against social engineering attacks.
The Importance of Understanding Psychology in Preventing Social Engineering Attacks
Understanding the psychological motivations and tactics used by social engineers can help protect against these attacks. By recognizing the psychological biases and heuristics that make individuals more susceptible to social engineering, we can develop targeted strategies to mitigate these risks. Effective defense against social engineering attacks requires a deep understanding of human psychology and behavior.
Final Wrap-Up
In conclusion, social engineering is a complex and multifaceted threat that requires a comprehensive understanding of human psychology and behavior. By recognizing the tactics, techniques, and procedures used by social engineers, individuals can take proactive steps to prevent and mitigate these attacks. Furthermore, educating employees and organizations on the dangers of social engineering can help to create a culture of awareness and vigilance, ultimately protecting against these types of threats.
FAQs
What is social engineering?
Social engineering is the practice of manipulating individuals into divulging confidential information or performing certain actions, often through psychological manipulation rather than technical means.
What are some common tactics used by social engineers?
Some common tactics used by social engineers include phishing, pretexting, baiting, and quid pro quo.
How can I protect myself against social engineering attacks?
By recognizing the tactics, techniques, and procedures used by social engineers, being cautious when interacting with unknown individuals or emails, and using robust security measures such as firewalls and antivirus software.
Can social engineering attacks be prevented?
While no system is completely secure, education and awareness can go a long way in preventing social engineering attacks. Employees and organizations can benefit from training on cybersecurity and social engineering awareness.
